How ControlUp & Laps Make Managing the Local Administrator Password Simple
Local administrator passwords are a huge challenge in organizations. If one gets exposed—whether through an employee leaving an organization, a laptop being stolen or some other event—changing the local administrator password is a huge hassle. A lot of IT shops leave the local administrator password as whatever was set from when Windows was installed (including if the installation was a silent, scripted install).
If the local administrator account credentials are compromised an attacker can access ANY machine with the same username/password combination. This includes file shares, VDI machines, multisession machines, database servers, and so on.
This is a serious issue.
Fortunately, Microsoft has an answer to this problem: the Local Administrator Password Solution (LAPS).
LAPS resolves this issue by setting a different, rotating, random password for the common local administrator account on every computer in the domain.
LAPS simplifies password management while helping customers implement additional recommended defenses against cyberattacks. In particular, the solution mitigates the risk of lateral escalation that results when customers use the same administrative local account and password combination on their computers. LAPS stores the password for each computer’s local administrator account in AD, secured in a confidential attribute in the computer’s corresponding AD object. The computer can update its own password data in AD, and domain administrators can grant read access to authorized users or groups, such as workstation help desk administrators.
How can ControlUp help?
ControlUp provides three script actions that you can use to manage LAPS.
- LAPS: Get Account Password
- LAPS:RDP to Local Admin Account
- LAPS: Reset Account Password
LAPS: Get Account Password
Users that are configured to read the password from LAPS can now get the password for the selected machine(s) in ControlUp. ControlUp displays the password and you can then log on or elevate with that credential.
LAPS: RDP to Local Admin Account
Automatically connect to the local administrator account of the target machine. If your organization prevents running a domain account in an administrator context, you can still leverage the local administrator account to do applications installs, configuration, and other things without exposing an elevated domain account. Simply RDP to the local admin account, do the work, then log off.
LAPS: Reset Account Password
Users with permissions to reset the LAPS account password can now do that through ControlUp. Select huge swaths of machines all at once! ControlUp reports back on the status of the update and whether or not it was successful.
It’s not working for me!
If you encounter any issues with the script actions, please ensure you have set up correct permissions! If the LAPS utility works, then so should ControlUp.
Your users and machines must be able to read and set the stored passwords stored in Active Directory. To set the proper permissions, right-click on the OU containing the machines that will be protected by LAPS and select “Properties.” Add a group with the users whom you want to be able to *read* passwords set by LAPS (I created a group called “CTX.LAPS”). Set the group to be able to READ the ms-Mcs-AdmPwd property. I created a short video demonstrating this process here:
How do I start using this feature?
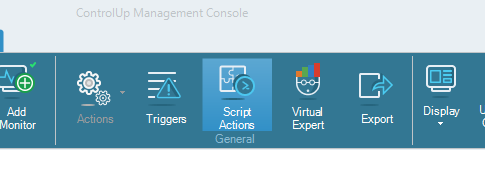
Simply go into your ControlUp Console and click the “Script Actions” button.
In the “Community Scripts” tab, find the published script actions with “LAPS” in their title and click the “Add Script” button.

Now, when you right-click on any machine you can search for “LAPS” within the search field and all of the actions will appear!
ControlUp has been making life simpler for the EUC community for years. But the least-guarded secret in the world is that the same capabilities are lifesavers for enterprise-class customers, too. No matter the size of your deployment, ControlUp is purpose-built to help you manage your infrastructure at scale.
New to ControlUp?
Download ControlUp for free to see how it can help monitor and manage your enterprise today!